MicroAge Richmond
Cyber Armor Built For Your Business
Reducing Risk Through Prevention + Jahan’s Three Rules of Computing.
Helping businesses across Richmond and Greater Vancouver stay secure, supported, and guided through what comes next.
Become Aware of Your risks And Protect Your Business.
ARE YOU LOOKING FOR MANAGED IT SERVICES?
Leave your "it" worries behind and focus on what really matters-
your business
Our expert team is here to manage your technology needs, so you don't have to. Book a free consultation
call today and discover the power of hassle-free IT

Why Kindhearted Businesses Choose
MicroAge Richmond?

Structured Technology Leadership
We help your business reduce risk, strengthen resilience, and build a more secure technology foundation for long-term growth.
Disciplined Cybersecurity Execution
We help your business move forward with greater clarity through thoughtful assessments, practical guidance, and layered Cyber Armor.

Kindhearted Business Owners
We believe the strongest businesses are built by people who care about their staff, their clients, and their community.

Why MicroAge?
MicroAge is your single source with the power and energy to help you accelerate
Your very own Virtual CIO to assist with identifying business risks, defining long-term strategy, and technology budgeting
Why MicroAge?
You'll experience rapid, systematic, and complete execution of your assessment with MicroAge's proven methodology and tools
Proactive consultation, including best practices assessment and alignment

Who We Help?
Financial Services
Healthcare
Manufacturing
Engineering
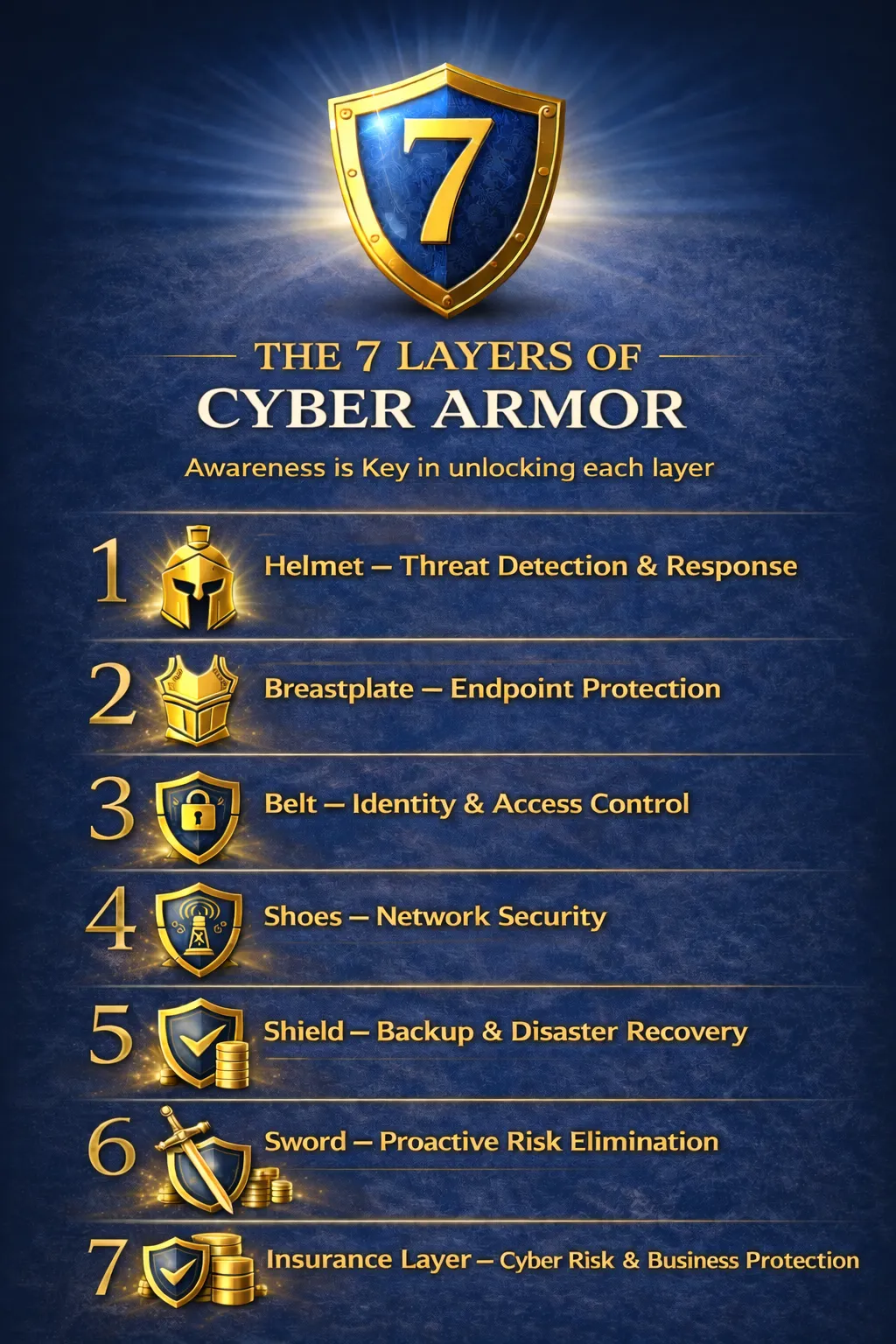
The 7 Layers of Cyber Armor
Awareness is Key
Strong businesses are built on awareness.
The 7 Layers of Cyber Armor shift your focus from reacting to threats to proactively strengthening your environment — so technology becomes a confident foundation for growth.
The Layers
Device
Detect and contain threats before they disrupt operations.
Endpoint
Protect against emerging risks so your team works without interruption.
Identity
Gain clear visibility into access — reducing exposure while preserving productivity.
Network
Structure and secure information flow with a resilient perimeter.
Backup
Ensure fast, reliable recovery when it matters most.
Proactive
Continuously assess and refine protection as your business evolves.
Each layer reinforces the next.
At MicroAge Richmond, we partner with leadership to bring structure, transparency, and disciplined execution across every layer.
Awareness creates stability.
Stability enables growth.
Growth becomes intentional.

About Us
Is managing your IT systems taking up too much of your valuable time?
Let us take care of it for you. Our team has been providing top-notch IT managed services to businesses like yours for over 25 years, both locally in the Greater Vancouver Area and across the US.
We pride ourselves on delivering customized solutions to meet the unique needs of each of our clients. With our expert help, you can free up your time and energy to focus on what really matters - growing your business.
Book a free consultation call today and discover how we can help you achieve your goals.
Operational Stability. Strategic Growth
Technology should not be a distraction.
It should be structured, predictable, and aligned with your objectives.
At MicroAge Richmond, we deliver:
Strategic IT Leadership
Planning, budgeting, and long-term technology alignment.
Managed IT & Infrastructure
Reliable systems, secure networks, and responsive support.
Cloud & Modern Workplace Solutions
Scalable environments built for flexibility and resilience.
Procurement & Deployment
The right technology implemented correctly — the first time.

FAQ's
How can we improve our network security and prevent cyberattacks
Some of buzz words you will hear is called Zero trust network. Here are some practical steps you can implement for your business.
1. Use password manager to manage passwords
2. Regularly update your operating system, software, and firmware to ensure that security patches are applied, and vulnerabilities are addressed.
3. Install and regularly update anti-virus and anti-malware software to protect against malicious software. Don’t rely on Defender or Mac OS is secure by design.
4. Enable two-factor authentication for all accounts that support it. This adds an extra layer of security by requiring a second form of verification, such as a text message or fingerprint scan.
5. Use a VPN when accessing the internet from public networks or when traveling. A VPN encrypts your internet traffic, making it more difficult for hackers to intercept.
6. Restrict access to sensitive information only to those who need it, and monitor access closely.
7. Provide Cyber Security Awareness training for the staff for best practices, such as how to identify and avoid phishing scams, and how to secure their devices and accounts.
8. Regularly audit your network security to identify vulnerabilities and ensure that all security measures are up to date.
What is the best way to back up and protect our data?
The best way to backup and protect is not to have to manually plug something to do it. Today we have cloud storage in Canada and US that comply with data privacy rules that can be used to backup files or mirror images of the whole enchilada aka your computer.
What are the best practices for managing and securing mobile devices in the workplace?
If you have emails in Microsoft 365, Microsoft InTune is a good solution. Google has its competitive solution as well. The key is someone has to monitor the reports and take actions or set alerts so appropriate staff are notified if and when suspicious activities happen.
What Are The Best Tools And Strategies For Monitoring And Managing Our IT Systems And Assets?
You have many options here. The key is not lock yourself to one provider for long term without Exit clause. Make the investment for the contract to be in your favour. The majority of the tools do the same tasks

FAQ's
How can we improve our network security and prevent cyberattacks?How can we improve our network security and prevent cyberattacks?
Some of buzz words you will hear is called Zero trust network. Here are some practical steps you can implement for your business.
1. Use password manager to manage passwords
2. Regularly update your operating system, software, and firmware to ensure that security patches are applied, and vulnerabilities are addressed.
3. Install and regularly update anti-virus and anti-malware software to protect against malicious software. Don’t rely on Defender or Mac OS is secure by design.
4. Enable two-factor authentication for all accounts that support it. This adds an extra layer of security by requiring a second form of verification, such as a text message or fingerprint scan.
5. Use a VPN when accessing the internet from public networks or when traveling. A VPN encrypts your internet traffic, making it more difficult for hackers to intercept.
6. Restrict access to sensitive information only to those who need it, and monitor access closely.
7. Provide Cyber Security Awareness training for the staff for best practices, such as how to identify and avoid phishing scams, and how to secure their devices and accounts.
8. Regularly audit your network security to identify vulnerabilities and ensure that all security measures are up to date.
What is the best way to back up and protect our data?
The best way to backup and protect is not to have to manually plug something to do it. Today we have cloud storage in Canada and US that comply with data privacy rules that can be used to backup files or mirror images of the whole enchilada aka your computer.
What are the best practices for managing and securing mobile devices in the workplace?
If you have emails in Microsoft 365, Microsoft InTune is a good solution. Google has its competitive solution as well. The key is someone has to monitor the reports and take actions or set alerts so appropriate staff are notified if and when suspicious activities happen.
What Are The Best Tools And Strategies For Monitoring And Managing Our IT Systems And Assets?
You have many options here. The key is not lock yourself to one provider for long term without Exit clause. Make the investment for the contract to be in your favour. The majority of the tools do the same tasks
Why work with us?
We've been partnering with businesses in the Greater Vancouver Area to help them achieve their business goals for over 25 years.
MicroAge Richmond helps your business move forward with thoughtful guidance, layered protection, and trusted local support
Gain the confidence of working with a Canadian technology partner backed by decades of experience supporting businesses across a wide range of industries
Your business does not have to navigate cybersecurity and technology challenges alone
Thoughtful technology guidance tailored to your business goals, security needs, and long-term growth
We help your business move forward with greater clarity through thoughtful guidance, layered protection, and technology decisions that support long-term resilience
Responsive support from a Canadian team that understands the needs of businesses across Richmond and Greater Vancouver
Thoughtful guidance to help your business prepare for future risks, reduce unnecessary complexity, and plan technology investments with greater confidence

Why work with us?
We've been partnering with businesses in the Greater Vancouver Area to help them achieve their business goals for over 25 years.
MicroAge is your single source with the power and energy to help you accelerate
Leverage our 25 years of experience delivering transformative network support for large, geographically dispersed networks
No need to expend time and resources to tackle it alone
Proactive consultation, including best practices assessment and alignment
You'll experience rapid, systematic, and complete execution of your assessment with MicroAge's proven methodology and tools
Unparalleled help desk support from our Canadian support team
Your very own Virtual CIO to assist with identifying business risks, defining long-terme strategy, and technology budgeting

Get the facts right about your IT
Receive a free evaluation of your IT environment and benefit from the understanding of one of our experts to take the right steps for your IT needs. The free consultation includes:
An evaluation of your IT environment
A one-on-one meeting with one of our experts
Network performance analysis
A preliminary evaluation of your cybersecurity state
Report, advice and recommendations for your business
Get the facts right about your IT
Receive a free evaluation of your IT environment and benefit from the understanding of one of our experts to take the right steps for your IT needs. The free consultation includes:
An evaluation of your IT environment
A one-on-one meeting with one of our experts
Network performance analysis
A preliminary evaluation of your cybersecurity state
Report, advice and recommendations for your business
© Copyright 2026. MicroAgeRichmond.com. All rights reserved.
© Copyright 2023. MicroAgeRichmond.com. All rights reserved.